Claude Code Governance: How To Govern Agent Rollouts with an AI Gateway
.png)
Built for Speed: ~10ms Latency, Even Under Load
Blazingly fast way to build, track and deploy your models!
- Handles 350+ RPS on just 1 vCPU — no tuning needed
- Production-ready with full enterprise support
Claude Code is no longer experimental. It reads entire codebases, edits files, runs terminal commands, executes tests, and iterates on solutions — all from natural language instructions. Engineering teams are rolling it out fast because the productivity gains are real.
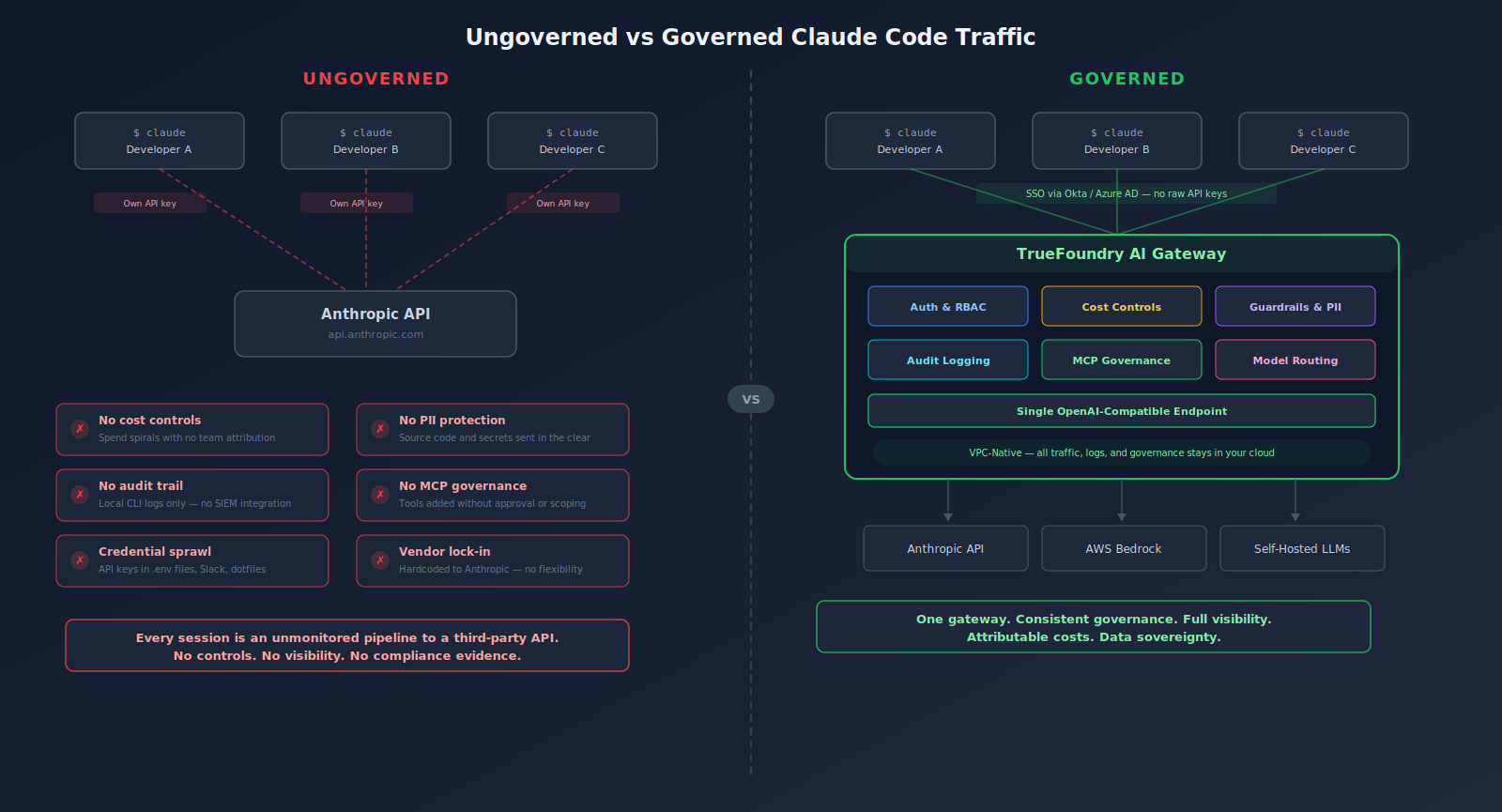
But every Claude Code session is also an unmonitored pipeline between your developers, your proprietary codebase, and Anthropic's API. Without centralized governance, that pipeline carries serious security, cost, and compliance risk.
This guide breaks down the specific risks of ungoverned Claude Code rollouts and shows how TrueFoundry's AI Gateway gives platform teams the control plane they need to govern Claude Code traffic at enterprise scale — without slowing developers down.
What Is Claude Code and Why Does It Matter for Enterprise Engineering?
Claude Code is Anthropic's agentic coding tool. Unlike traditional code-completion assistants that suggest the next line in an editor, Claude Code operates as an autonomous agent. It can:
- Read entire codebases and navigate across multiple directories
- Write, modify, and delete files
- Execute shell commands and interpret error output
- Run tests and iterate on failures
- Connect to external tools via the Model Context Protocol (MCP)
- Maintain project-level memory through CLAUDE.md configuration files
It runs in the terminal, in IDEs like VS Code and JetBrains, through a desktop app, and in the browser. It works with models across the Claude family — Opus 4.6, Sonnet 4.6, and Haiku 4.5. Enterprise customers can also access it through Amazon Bedrock or Google Cloud Vertex AI.
The adoption numbers reflect the impact. Stack Overflow's 2025 Developer Survey found that 85% of developers already use or plan to use AI coding tools. Gartner predicts that 75% of hiring processes will include AI proficiency testing by 2027. AI-assisted coding is becoming standard development infrastructure.
For a detailed look at how Claude Code actually processes tasks from context ingestion to iteration, see our Claude Code workflows guide.
The Business Risks of Ungoverned Claude Code Rollouts
Enterprise-wide adoption of Claude Code doesn't just produce productivity gains. It also produces a new category of LLM traffic — high-volume, high-context, and deeply tied to proprietary source code. Without governance, five risks compound fast.
Uncontrolled Cost Exposure
Claude Code sessions consume tokens aggressively. Referencing five medium-sized files in a single session can burn through 30,000+ tokens. Developers iterating on complex refactors may generate hundreds of API calls per day. Claude Code itself has no organizational budget controls — that responsibility falls to whatever sits between the developer and the API. Without centralized enforcement, costs spiral before finance even sees the invoice.
Sensitive Data Leakage
Claude Code sends code context to Anthropic's servers for processing. Proprietary source code, environment variables, API keys, configuration files, and potentially customer data all travel over the network. Security researchers have already identified real vulnerabilities — CVE-2025-54794 (path restriction bypass) and CVE-2025-54795 (command injection) were patched, but they demonstrate the attack surface. Without a governance layer inspecting outbound traffic, organizations have limited ability to enforce data loss prevention.
No Audit Trail
Regulated industries need clear records of AI usage: what was sent, what was returned, which models were used, by whom, and when. Claude Code out of the box does not produce the centralized, structured audit logs that compliance teams require. Every ungoverned session is a blind spot. When an auditor asks, "what did your AI coding tool access last quarter?" — you need a better answer than "we don't know."
Shadow AI Proliferation
Without governance, developers find their own paths. Different teams configure Claude Code differently. They use different models, apply different security practices, or bypass organizational controls entirely. Shadow AI fragmentation makes it impossible to enforce consistent security policies, accurately forecast costs, or demonstrate compliance across the org.
Model and Provider Lock-In
Without an abstraction layer, organizations hardcode workflows directly to Anthropic's API. If pricing changes, models are deprecated, or the team wants to evaluate alternatives — migration gets expensive and disruptive. An enterprise that ties every developer's tooling to a single provider has surrendered negotiating leverage and architectural flexibility.
CRO Banner Title: Your Developers Are Already Using Claude Code — Who's Governing the Traffic?
Subtext: TrueFoundry's AI Gateway gives platform teams centralized auth, cost controls, guardrails, and audit logging for every Claude Code session
CTA: Book a Demo
Why the AI Gateway Pattern Solves Claude Code Governance
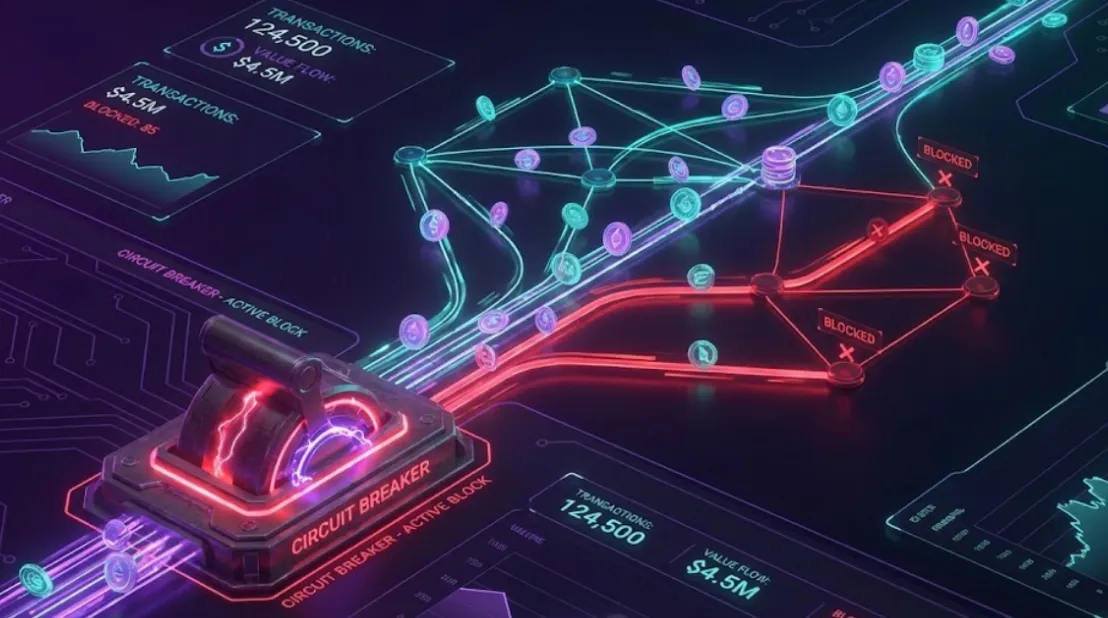
The AI gateway pattern addresses these risks by inserting a centralized control plane between all AI-consuming applications (including Claude Code) and the models they call. It is the same architectural principle that API gateways brought to REST and gRPC traffic — now extended to handle the specific requirements of LLM workloads.
An AI gateway sits in the request path and enforces governance at the infrastructure layer:
- Authentication and access control — developers never hold raw API keys
- Rate limits and token budgets — per-developer, per-team, or per-project caps prevent runaway costs
- Prompt and response logging — structured audit trails for every session
- Content filtering and PII detection — data loss prevention at the network layer
- Observability — real-time dashboards with AI-specific analytics
- Provider abstraction — route traffic across models and providers without changing client configurations
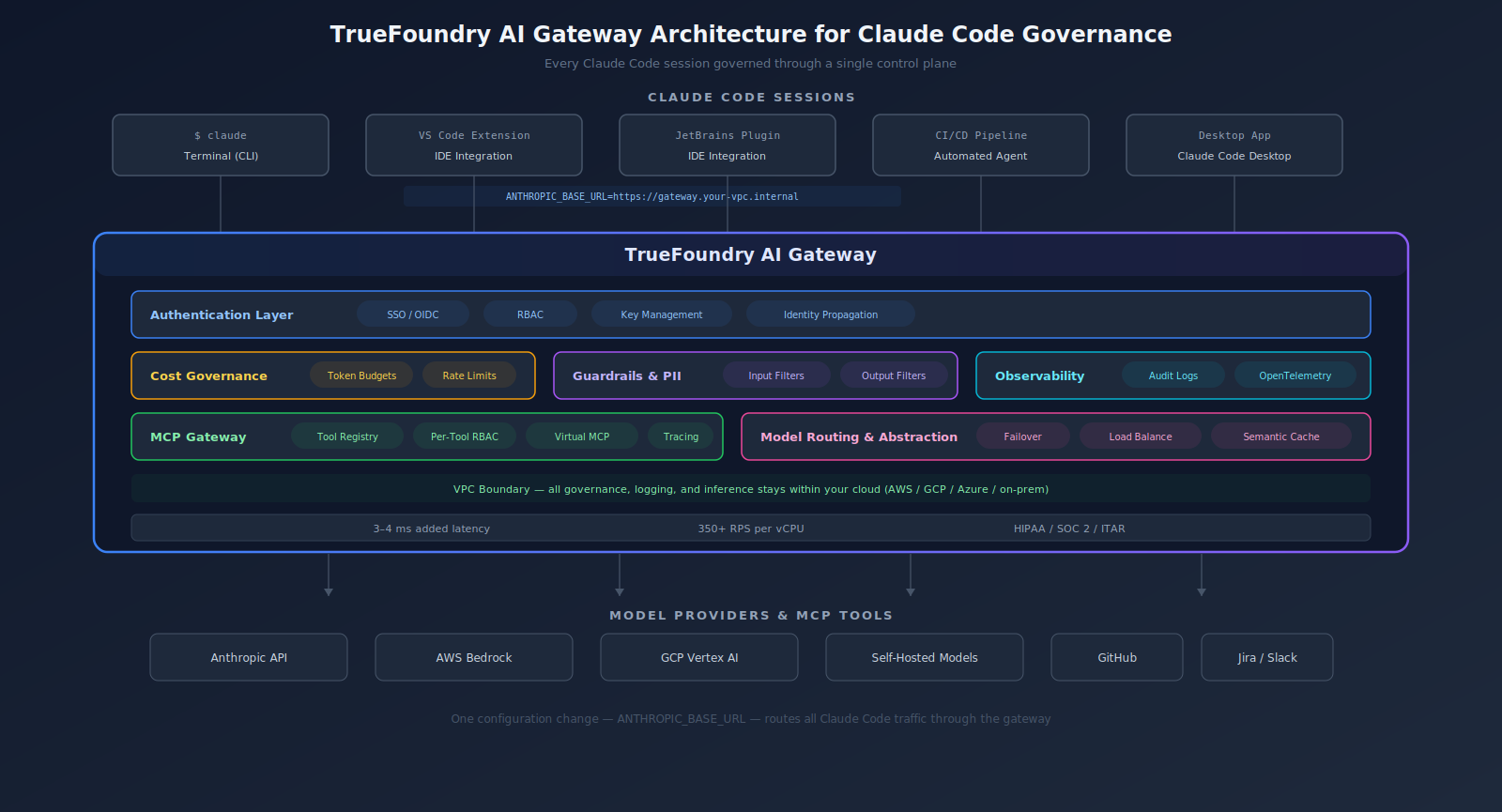
For Claude Code specifically, the AI gateway pattern is a natural fit. Claude Code communicates with Anthropic's API over standard HTTP. Routing that traffic through a gateway requires no changes to the developer's workflow — just a configuration change that points Claude Code to the gateway endpoint instead of directly to Anthropic.
The architectural pattern is now the industry consensus. Gartner's Hype Cycle for Generative AI 2025 identifies AI gateways as critical infrastructure for scaling AI responsibly. TrueFoundry was recognized in Gartner's 2025 Market Guide for AI Gateways as an emerging solution provider in this category.
How TrueFoundry AI Gateway Governs Claude Code Traffic
TrueFoundry's AI Gateway provides enterprise-grade governance, security, and observability for LLM traffic — including traffic from Claude Code sessions. It goes beyond traditional API gateway capabilities with AI-native controls built specifically for LLM and agentic workloads.
Centralized Authentication and Key Management
With TrueFoundry's gateway in the path, individual developers never hold or manage Anthropic API keys. The gateway injects authentication headers on behalf of the developer, using credentials managed centrally by the platform team. Developers authenticate once through your existing identity provider (Okta, Azure AD, Auth0) via SSO, and the gateway handles all downstream provider auth.
The result: no credential sprawl, simplified key rotation, and no API key leakage through developer workstations, .env files, or Slack messages.
Per-Team Cost Controls and Token Budgets
TrueFoundry enforces hard spending limits per team, per developer, and per endpoint. The gateway tracks token consumption — prompt tokens, completion tokens, total cost — for every request in real time.
Platform teams can:
- Set monthly or daily budget caps with configurable alert thresholds
- Auto-throttle or block requests when limits are reached
- Break down spend by team, project, model, or individual developer
- Run chargeback reporting without exporting logs to external tools
For more on building cost governance into the AI layer, see our FinOps for AI guide.
Composable Guardrails and PII Protection
TrueFoundry's guardrails engine operates on both inputs and outputs at the gateway layer. For Claude Code traffic specifically, this means:
- Input guardrails scan prompts before they reach Anthropic — masking PII, redacting API keys, blocking prohibited content patterns
- Output guardrails filter model responses before they reach the developer — enforcing content policy and detecting unsafe outputs
Each rule operates in validate (block) or mutate (modify) mode. Platform teams configure guardrails centrally. Every Claude Code session inherits them automatically — no per-developer configuration needed.
Traffic Observability and Audit Logging
Every Claude Code request routed through the gateway produces structured log records: user identity, model used, token counts, latency metrics, guardrail firing events, and cost attribution. Logs stay within your infrastructure and export to your existing observability stack — Grafana, Datadog, Splunk, or any OpenTelemetry-compatible target.
When compliance asks, "who used Claude Code to modify production configs last Tuesday?" — the gateway has the answer.
MCP Governance for Tool Access
As Claude Code's MCP integration deepens — connecting to tools like GitHub, Jira, Slack, Confluence, and Datadog — TrueFoundry's MCP Gateway extends governance to tool traffic:
- Centralized MCP registry with per-tool RBAC
- Federated authentication so developers connect to the gateway, not individual servers
- Virtual MCP Servers that scope which tools each agent (or developer session) can access
- Full tracing of every tool call, including what data was sent and returned
Without MCP governance, every new tool connection a developer adds expands the attack surface. Our enterprise MCP access control guide covers the full implementation pattern.
VPC-Native Deployment with Full Data Sovereignty
Here's where TrueFoundry diverges from SaaS-first gateways. TrueFoundry deploys within your AWS, GCP, or Azure account. It also supports on-premises and air-gapped deployments.
All inference traffic, governance logic, audit logs, and observability data stay within your cloud boundary. No prompts, code context, or usage data leave your infrastructure. For enterprises in healthcare, defense, financial services, or any regulated industry with strict data residency requirements — this is the difference between "we can use Claude Code" and "we can't."
TrueFoundry satisfies HIPAA, SOC 2, and ITAR requirements out of the box. The gateway adds roughly 3–4 ms of latency per request, with each proxy instance handling 350+ requests per second on a single vCPU.
Provider Abstraction and Model Routing
TrueFoundry's gateway provides a universal LLM API across 250+ models. Start with Claude Code on Anthropic's API today. Route traffic to Bedrock-hosted or Vertex-hosted Claude models tomorrow. Swap in GPT-4 or a self-hosted Llama model for specific use cases. No developer workflow changes required — just a gateway configuration update.
CRO Banner Title: Claude Code Is a Powerful Agent — Your Gateway Should Govern It Like One
Subtext: Route all Claude Code traffic through TrueFoundry's AI Gateway for centralized cost controls, guardrails, audit logging, and MCP governance
CTA: Start Free
Direct API vs AI Gateway: A Governance Comparison

Get Started Governing Claude Code
Your developers are already using Claude Code. The question is whether that traffic is governed — or whether every session is an unmonitored pipeline to a third-party API.
TrueFoundry's AI Gateway gives platform teams a single control plane for all Claude Code traffic: centralized auth, per-team cost limits, composable guardrails, structured audit logs, MCP governance, and full data sovereignty. VPC-native. SOC 2 and HIPAA ready.
Book a Demo to see how TrueFoundry governs Claude Code at enterprise scale. Or start free with a live sandbox — no credit card required.
TrueFoundry AI Gateway delivers ~3–4 ms latency, handles 350+ RPS on 1 vCPU, scales horizontally with ease, and is production-ready, while LiteLLM suffers from high latency, struggles beyond moderate RPS, lacks built-in scaling, and is best for light or prototype workloads.
The fastest way to build, govern and scale your AI


Govern, Deploy and Trace AI in Your Own Infrastructure
Recent Blogs
Frequently asked questions
How do I route Claude Code through TrueFoundry's AI Gateway?
Set the ANTHROPIC_BASE_URL environment variable to your TrueFoundry gateway endpoint. The gateway handles authentication with Anthropic's API on your behalf. No changes to the Claude Code CLI or developer workflow required — just a configuration update.
Can TrueFoundry prevent developers from sending sensitive code to Anthropic?
Yes. The guardrails engine scans every outbound request at the gateway layer. You can configure rules to detect and redact API keys, customer PII, internal project names, or any regex pattern — before the request ever leaves your infrastructure.
Does using an AI gateway add noticeable latency to Claude Code sessions?
TrueFoundry adds roughly 3–4 ms per request. Compared to LLM inference times (often several seconds), the overhead is negligible. Semantic caching can actually reduce total round-trip time for repeated queries.
How does TrueFoundry help with Claude Code audit compliance?
The gateway captures structured log records for every request — user identity, model, tokens, latency, cost, and guardrail events. Logs stay in your infrastructure and export to Grafana, Datadog, Splunk, or any OpenTelemetry target. No scattered local logs on developer machines.
What makes TrueFoundry different from other AI gateways for Claude Code governance?
VPC-native deployment. TrueFoundry runs inside your AWS, GCP, or Azure account. All traffic, logs, and governance data stay within your cloud boundary — satisfying HIPAA, SOC 2, and ITAR requirements that SaaS-first gateways cannot meet. Combined with native MCP Gateway support, per-team FinOps controls, and composable guardrails, TrueFoundry provides the full governance stack for Claude Code at enterprise scale.



















.webp)




.webp)
.webp)
.webp)
.webp)
.webp)














