MCP Authentication in Claude Code 2026 Guide
.png)
Built for Speed: ~10ms Latency, Even Under Load
Blazingly fast way to build, track and deploy your models!
- Handles 350+ RPS on just 1 vCPU — no tuning needed
- Production-ready with full enterprise support
What is MCP?
MCP (Model Context Protocol) is an open standard developed by Anthropic that allows Claude Code to communicate with external systems in a structured way.
Instead of stuffing tool logic into the prompt, MCP creates a clear middleware layer. Claude calls the tool in a standard format. The MCP server receives the request and forwards it to the real system behind it, such as a database, internal API, cloud service, or ticket management system.
You can think of the MCP server as an adapter layer. One side is Claude Code. The other side is your physical infrastructure. It helps both sides understand each other without having to rewrite everything from scratch every time an integration occurs.
Without MCP, Claude Code only responded to text. With MCP, it begins to interact with the real system. And from that point on, it's no longer just "AI answering for fun."
Why MCP authentication matters
As MCP becomes more popular, I see many people using Claude Code to connect directly to internal systems. Some just call API tests. Others connect directly to services running on AWS with tight IAM.
The problem is: as soon as Claude can call the tool, it represents some kind of identity within your system.
If the authentication configuration is loose, the risk won't appear immediately. It's insidious. Like when I debugged a CloudFront configuration at. It was just a seemingly harmless forward header rule. No 500 errors, no downtime. But in reality, the access boundary was expanded more than expected. You have to carefully examine the logs to find the problem.
The same applies to MCP. If you choose the wrong authentication method, you could inadvertently:
- Expose your long-term API key
- Distribute access keys to multiple different users
- Grant Claude too many privileges than necessary.
Connecting to a manufacturing database or financial system on AWS will no longer a minor issue
Therefore, choosing the right authentication method isn't just about "getting the connection working." It can determine the security and consistency of the entire system behind it.
Why is authentication the first thing to consider?
These external tools are far from "harmless." They can contain source code, client records, production data, and internal tickets. But when Claude connects via MCP, it's not just reading for fun. It is acting as a verified identity deep inside your system. If the authentication is weak, you could be attacked. No complex attack is needed. One leaked API key is all it takes for things to go south very quickly.
The situation I encountered was similar. The service only provides a single token for both the development and production environments. Everything would be fine if that token information wasn't leaked during testing of a repository. Therefore, we need to change login credentials for both the production and development environments to avoid problems arising as soon as they are discovered. So, the system itself isn't the problem; the crucial issue lies in how you manage permissions. Authorization isn't just an add-on; it determines what Claude can do within its permitted scope, preventing security risks.
What is this article addressing?
Claude Code supports several different authentication methods. For example:
- API key
- Bearer token
- OAuth
- AWS credential (Access Key or assume role)
It's confusing at first glance. Each method exists for its own reason. There is no "right way for all cases."
Choosing the wrong method can lead to:
- Credential exposure
- Needing to re-configure midway
- Team wasting time fixing workflows
I once configured an MCP server running behind an API Gateway on AWS.
Initially, I used long-term access keys to speed up access. However, I realized this wasn't ideal compared to sharing keys with multiple testers for easy access. Ultimately, I switched to role-based assumptions to more clearly define permissions.
This article will delve into each point, explaining when to use each different method. The goal is to help you make the right choice from the start, avoiding future modifications.
Installing Claude Code
If you haven't installed Claude Code yet, you can set it up quickly.
macOS, Linux, WSL:
curl -fsSL https://claude.ai/install.sh | bashWindows PowerShell:
irm https://claude.ai/install.ps1 | iexMacOS Only
brew install --cask claude-codeNow move to the next sections about the authentication security
Defining Security in a CLI Environment
When running a CLI on a local machine, many people only think about HTTPS. Actually, the bigger issue lies in how you maintain your credentials.
HTTPS only protects data during transmission. It doesn't help if the token is exposed on your machine. In a CLI environment, the main issues are:
- Where do you store the key?
- How long does the token last?
- Who can use it?
Low security is when you leave a long-term API key in a plaintext config file. If that file is accidentally committed to the repository, it's over. That key is essentially out of control. And because it's a long-term key, you have to manually rotate it.
I once encountered a similar situation while debugging an environment issue with ECS. I was using the Amazon ECS MCP Server with an access key and secret key. After that, I forgot about those credentials. A few days later, I asked Claude to investigate some issues in another environment, but it was still using the old credentials, so it ended up performing many actions in the production environment.
High security is different. You use short-term tokens. Or referencing via environment variables. Or using service-level authentication mechanisms like IAM roles. For example, when using AWS SSO, tokens have a clear expiration date. After expiration, you have to log in again. If the machine is compromised, the attacker only has a very short window to do something. This method isn't perfect. But it minimizes damage if something goes wrong.
Below are four common authentication configuration methods for MCP servers in Claude Code. Each method is suitable for a different context.
1. Static HTTP Headers (API Keys & Bearer Tokens)
This is the easiest method to get started. This way will work well with many third-party services that use long-term API keys or Private Access Tokens (PATs).
Command Line Configuration
If you want to quickly add an MCP server with an authentication header, just use “claude mcp add” and pass “--header”
# Add a weather service MCP server with Bearer Token authentication
claude mcp add weather-service \
--transport http \
--header "Authorization: Bearer secret-token-123" \
https://api.weather-data.com/mcpWhen the process is complete, Claude will automatically write the configuration for you. No manual steps are needed. “Claude/settings.json”. This method is very convenient for quickly checking an external service.
I often use it when I need to test an API before officially integrating it into the system. Just remember one thing: Don't paste the actual token into the command and then commit the shell history somewhere. That happens more often than you think.
Configuration File (.claude/settings.json)
If don't want to put the token code in the file as plain text, you can use an environment variable.
Claude will read “${ENV_VAR}” and replace it with the actual value when the CLI starts.
For example:
{
"mcpServers": {
"data-tool": {
"url": "https://api.myservice.com/mcp",
"type": "http",
"headers": {
"Authorization": "Bearer ${APP_API_TOKEN}",
"X-Org-Id": "org-888"
}
}
}
}
This method is safer than writing the token directly to the file. You just need to export the environment variable before running Claude.
I once saw an internal repository accidentally commit a token to the config. Initially, I thought it was a private repository, so it was fine. Then the repository was shared with another team for testing. The production token was also included. Using environment variables doesn't solve all risks. But at least it reduces the chance of key exposure when committing by mistake.
Advantages:
- Easy to configure.
- Suitable for quick integration with external services.
Disadvantages:
- The token is still a long-term type.
- If exposed, you have to manually rotate it.
2.1 AWS MCP Credentials
2.1 Acess Key and Secret Key (for AWS-hosted MCP Servers)
If your MCP server is located at AWS, this is much more practical. You can use the existing AWS login credentials on your machine. Typically, this is configured via AWS configure or AWS SSO. Claude will inherit variables like:
- AWS_ACCESS_KEY_ID
- AWS_SECRET_ACCESS_KEY
- AWS_SESSION_TOKEN
- AWS_PROFILE
This is very available when the MCP server runs behind an API Gateway. Or when the backend is on Lambda or ECS and IAM authentication is enabled.
Such as, configuring an MCP proxy to sign requests using Signature V4:
{
"mcpServers": {
"cloud-logger": {
"command": "node",
"args": ["/path/to/aws-mcp-proxy.js"],
"env": {
"AWS_PROFILE": "my-dev-profile",
"AWS_REGION": "ap-southeast-1",
"MCP_ENDPOINT": "https://my-mcp-service.execute-api.ap-southeast-1.amazonaws.com/prod"
}
}
}
}
Or, more simply, export environment variables before running Claude:
# Set AWS credentials before running Claude Code
export AWS_PROFILE=my-dev-profile
export AWS_REGION=ap-southeast-1# Start Claude Code — the MCP server will use these credentials claude
Claude doesn't need to know the key details. It only uses the AWS context you're logged into.
I remember debugging an internal MCP server running behind an API Gateway. Requests were consistently returning 403 errors. At the time, I thought it was a policy issue. But then I discovered that the AWS SSO certificate on my machine had expired. Simply running the “aws sso login” command again fixed everything. Since then, I've always noted that registered services need to check the session before working on them, rather than blaming IAM.
Advantages:
- Tokens are usually short-term via STS.
- Can be automatically rotated.
- Higher security than long-term API keys.
Disadvantages:
- Dependent on AWS login status.
- Everything stops immediately once the session ends.
2.2. IAM Role Assumption (Least Privilege Access)
When you use AWS credentials directly, Claude is acting under your personal identity. That's convenient, but not always the right way. Assume a Role allows the MCP to use a separate identity. This identity only serves a specific machine or service. This is very useful when you want to simulate production.
For example, testing how a service works with read-only access. Or when the MCP server only accepts a fixed IAM Role. It doesn't allow individual users to call it directly.
I encountered a case like this. An internal API only allowed backend roles to access it. Individual users were blocked. To test locally, you had to assume that specific role.
The workflow is quite clear:
- You request to assume an IAM Role.
- AWS STS checks if you have the permission to use sts:AssumeRole. If valid, STS returns a temporary credential.
- The MCP proxy will use that temporary credential to call the target service. The service only sees the role, not your individual user.
What I like about this method is the very clear permissions. Roles have their own policies. If you want to impose any restrictions, you can adjust them in that policy. The downside is that initial configuration is a bit time-consuming. If the Trust policy is wrong by even one line, the assumption won't work. And debugging IAM is never a fun task.
Configuration Example
{
"mcpServers": {
"finance-bot": {
"command": "node",
"args": ["/path/to/aws-role-mcp-proxy.js"],
"env": {
"ASSUME_ROLE_ARN": "arn:aws:iam::123456789012:role/mcp-finance-bot-role",
"AWS_REGION": "ap-southeast-1",
"MCP_ENDPOINT": "https://secure-finance.execute-api.ap-southeast-1.amazonaws.com/prod"
}
}
}
}
Setting up IAM permissions to assume roles
To assume a role, your current user must have that permission. Without the correct trust policy, everything will stop immediately.
Usually, I'll define a few variables for simplicity:
# Define variables
export ACCOUNT_ID="123456789012"
export ROLE_NAME="mcp-finance-bot-role"
export MY_USER_ARN="arn:aws:iam::${ACCOUNT_ID}:user/developer@company.com"# Update the role's trust policy to allow your user to assume it
aws iam update-assume-role-policy \
--role-name "${ROLE_NAME}" \
--policy-document '{
"Version": "2012-10-17",
"Statement": [{
"Effect": "Allow",
"Principal": {"AWS": "'"${MY_USER_ARN}"'"},
"Action": "sts:AssumeRole"
}]
}This section essentially does only one thing. It tells AWS that your user is allowed to assume that role.
I once wasted almost a whole afternoon just because I was missing the correct ARN in the trust policy. The policy attached to the role was correct. But the trust policy didn't allow the user to assume. As a result, STS kept returning an AccessDenied error. Another point to remember:
IAM has a small delay. After updating the policy, you might have to wait a minute or two for it to take effect. If testing immediately still fails, don't panic.
Advantages:
- Maintains the minimum permissions principle.
- Everything a role can do is within its policy.
Disadvantages:
- The configuration is a bit complicated.
- Just one small mistake and it won't work.
3. Built-in OAuth 2.0 Support
For complex third-party services like GitHub, Linear, or Slack, an API key isn't enough. They require login via a standard user flow. Claude Code provides built-in OAuth support for these types of MCP servers.
Shell Commands
You don't need to write your own login flow. Before you start, you can check which servers require authentication:
# List the MCP servers that need authentication
claude mcp listIf you see any servers that aren't logged in, simply run:
# Start the login flow for a GitLab MCP server (opens browser)
claude mcp auth gitlab-serverInteractive Commands
There's a convenient feature. If you're using Claude and encounter a permissions error, you don't need to exit. You can authorize directly within the chat session.
Example:
>>> You: List my todos.
>>> Claude: I need access to Linear.
>>> /mcp auth linear-server
Just type that command. Claude will reactivate the login flow. Usually, it will open the browser for you to confirm permissions.
I once encountered a situation where the Linear token expired while I was reviewing an issue. Claude reported insufficient permissions midway through.
Instead of restarting the CLI, I just ran “/mcp auth” and it was done. I returned to work immediately afterward.
Advantages:
- Standard OAuth flow.
- Tokens are automatically refreshed.
- A fairly smooth experience when working with a user.
Disadvantages:
- Occasionally, you still have to open the browser and log in again. Especially when switching computers or when the login session ends.
Summary
Choosing which authentication method depends on two things:
- Where you store your credentials.
- And what problem you're solving.
There is no “best for all places” option. Only the one that fits the context. A small but important note: Make sure your Node.js environment is stable first. Finally discovered that the local machine was using the wrong Node version. Simply changing it to “nvm use" should work normally. Using nvm helps avoid many inexplicable errors due to environment mismatches. Don't underestimate this.
Quick Guide: Adding MCP Servers in Claude Code
HTTP Transport with Auth Header
# HTTP transport with auth header
claude mcp add my-server \
--transport http \
--header "Authorization: Bearer ${MY_TOKEN}" \
https://my-mcp-server.com/mcp
# Stdio transport (local process)
claude mcp add my-local-server \
-- node /path/to/server.js
# List configured MCP servers
claude mcp list# Remove an MCP server
claude mcp remove my-serverJust remembering these commands is enough to get started. The rest is about choosing the right authentication method for the right situation.
Frequently Asked Questions
How to generate Claude Code MCP OAuth token?
To generate a Claude Code MCP OAuth token, you typically integrate with an OAuth provider that issues short-term access tokens. This highly secure method helps prevent direct exposure of long-term credentials for your Claude Code MCP connections. The specific steps depend on your chosen OAuth provider's setup and its integration with Claude Code.
Can Claude Code access MCP servers?
Yes, Claude Code can access MCP servers, enabling interaction with external systems like databases and APIs. This functionality transforms Claude Code from a text responder to an active system participant. Effective claude code mcp authentication is vital for secure operations, preventing unauthorized access and ensuring data integrity across US infrastructure.
How to authenticate figma MCP in Claude Code?
To authenticate Figma MCP in Claude Code, you'll need to choose a secure claude mcp authentication method. This typically involves using API keys, OAuth, or Bearer tokens, depending on Figma's integration and your security policies. Focus on granting minimal privileges and avoiding long-term keys to ensure secure system interaction.
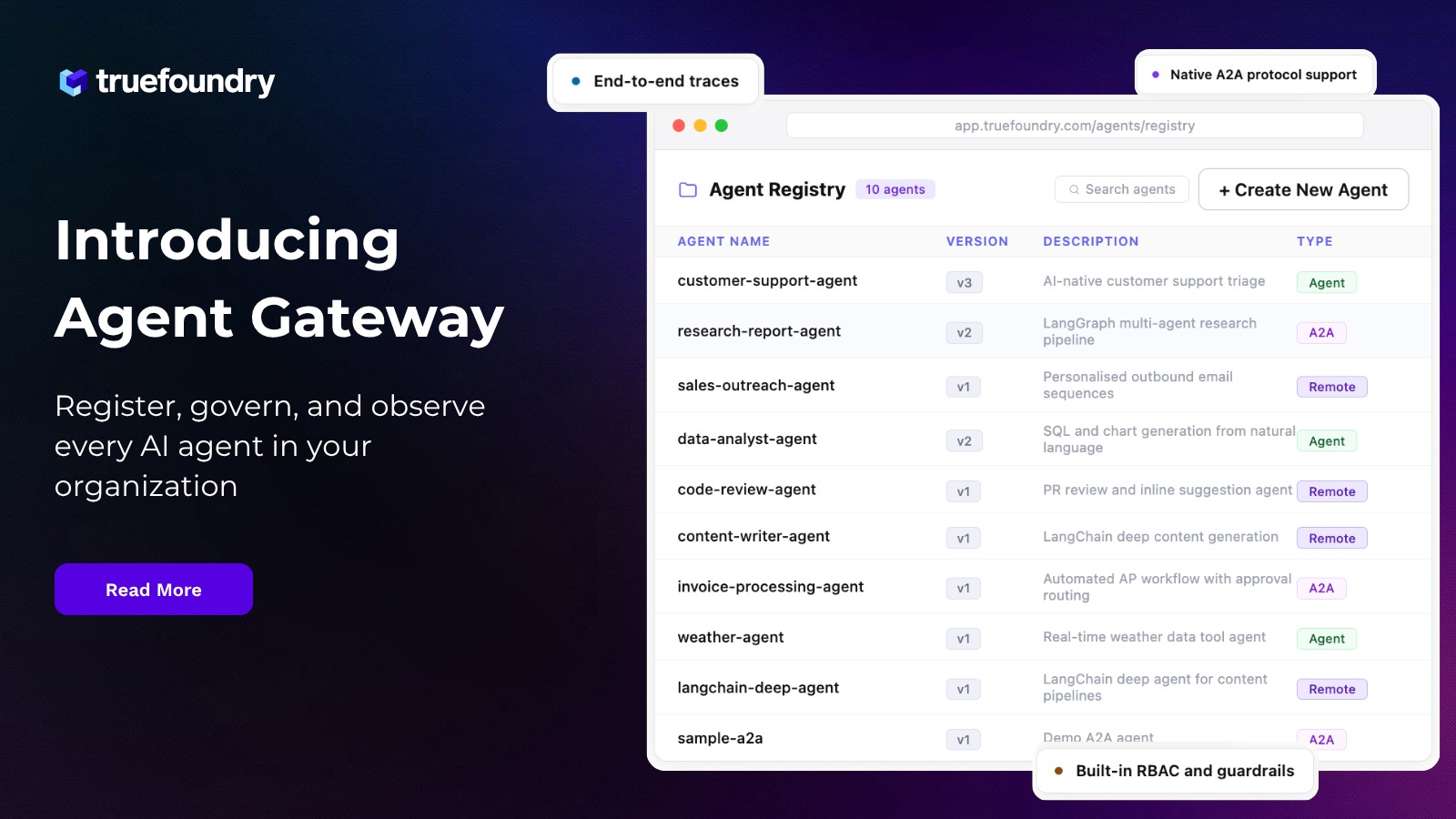
TrueFoundry AI Gateway delivers ~3–4 ms latency, handles 350+ RPS on 1 vCPU, scales horizontally with ease, and is production-ready, while LiteLLM suffers from high latency, struggles beyond moderate RPS, lacks built-in scaling, and is best for light or prototype workloads.
The fastest way to build, govern and scale your AI
















%20(28).webp)






.webp)
.webp)